Cyber security of electronic security systems remains a top concern for organizations.
Cyber security of electronic security systems remains a top concern for organizations.
Bosch and Genetec held a joint presentation at ISC West 2018 on cyber security to help attendees understand the solutions available to secure their systems.
Below are the documents and videos used in the session to further explain data and device security as related to the electronic security industry, in this case, specifically IP cameras and communication with the video management system. Plus, many questions were raised by the audience which prompted the informative Q&A document.
 Bosch and Genetec End-to-end Security PowerPoint
Bosch and Genetec End-to-end Security PowerPoint
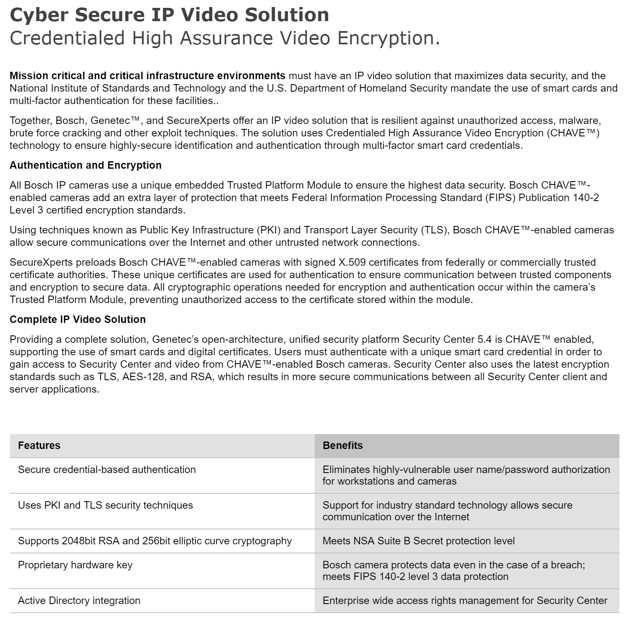
 Bosch and Genetec End-to-end Security Leaflet
Bosch and Genetec End-to-end Security Leaflet
 Bosch and Genetec End-to-end Security Video
Bosch and Genetec End-to-end Security Video
 Bosch CHAVE Video Security Video
Bosch CHAVE Video Security Video
 Bosch and Genetec End-to-end Security Q and A
Bosch and Genetec End-to-end Security Q and A
 New Training Course on Cyber Security
New Training Course on Cyber Security
A new two-day classroom course - Cyber Security and IP Video - provides demonstrations and in depth practical applications for fundamental vulnerability scanning as well as device and system lockdown procedures. After completing this course, attendees will understand the differences between vulnerability assessments and penetration testing, and be able to leverage scan information to reduce attack surfaces of system devices. Register Here
 We've summarized the information and many of the cyber security resources to help you stay on top of this topic:
We've summarized the information and many of the cyber security resources to help you stay on top of this topic:
- IP Video and Data Security Guidebook
- Secure the Edge of the Network - White Paper
- 3 Common Security Hacks
- Data Security Leaflet
- Securing Data and Equipment Racks
- Encryption of Intrusion Detection Systems
- Security of Security
- Security Encryption and Certificates FAQ
- PKI CHAVE One-Page
- PKI CHAVE Leaflet
- PKI CHAVE Presentation PPT
- Lessons learned from major health care data breaches
- NIST National Cybersecurity Center of Excellence
- Contact our team for expert security advice