What security professionals should ask security device manufacturers...
As more security cameras and IoT devices are connected to enterprise, government, and critical infrastructure networks, security and IT professionals are asking an important question: how can they trust that the device being installed has not already been compromised before it ever reaches the network?
In this discussion, Tom Fontana speaks with Sachin Khanna, IQSIGHT's Vice President of Product Management, about the growing importance of cybersecurity not only in device software and network configuration, but also throughout the entire product lifecycle. The message is clear: cybersecurity begins long before a camera or sensor is powered on. It starts in design, manufacturing, sourcing, shipping, warehousing, and supply chain verification.
Cybersecurity Starts Before the Device Reaches the Network
One of the most important points in the conversation is that today’s networks often contain more IoT devices than traditional computers. That shift changes the risk profile for security professionals. A vulnerable device is no longer just an operational concern. It can become a cybersecurity concern as well.
Sachin explains that organizations should think about the security of a device before it is connected to their network. For government, enterprise, and critical infrastructure customers, that means asking manufacturers and suppliers direct questions about how their devices are built, sourced, protected, and validated before shipment.
If a device is compromised during manufacturing, shipping, or storage, the problem may not be visible at installation. The device may appear normal at first, yet still carry a hidden long-term risk.
The Supply Chain Is Now Part of the Security Conversation
Supply chain security has become inseparable from device security. Customers should not only evaluate product features. They should also evaluate how a manufacturer manages component sourcing, factory cybersecurity, shipping integrity, and tamper prevention.
Sachin notes that supply chain attacks can happen at multiple stages. Components could be counterfeit. Products could be altered during manufacturing. Devices could be tampered with in transit or while sitting in a warehouse. Because of that, buyers need confidence that the manufacturer is maintaining a secure chain of trust from the original supplier all the way to final delivery.
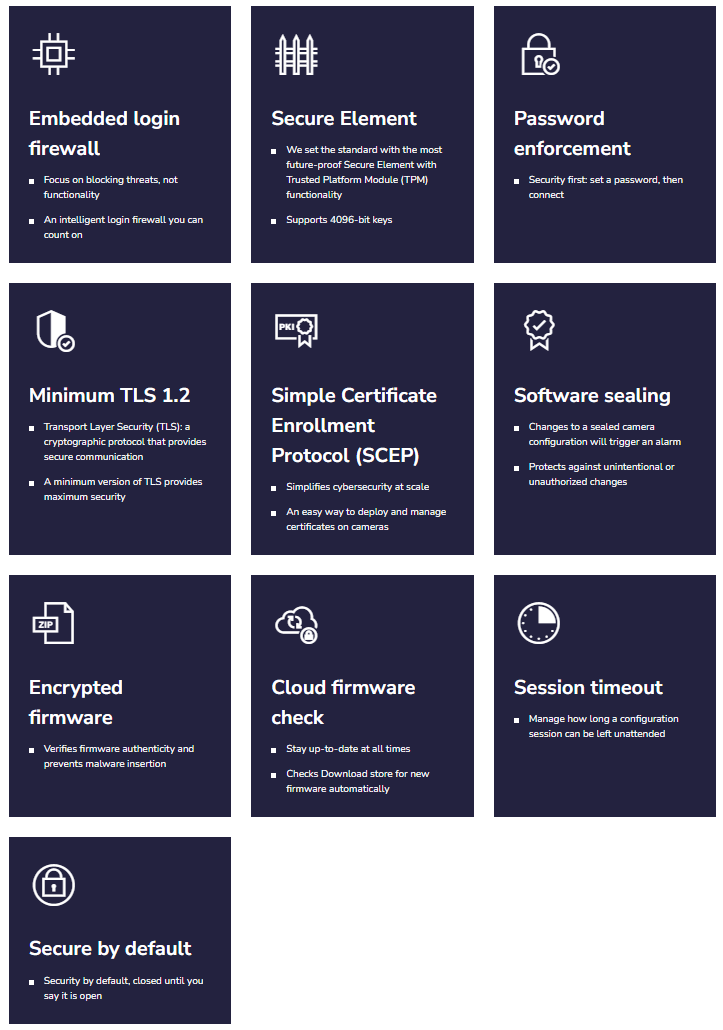
IQSIGHT’s approach, according to Sachin, is built around end-to-end cybersecurity. That includes strong cryptographic protections, signed firmware, secure hardware, and processes designed to verify that the device a customer receives is the same trusted device that left the manufacturer.
He also describes visible tamper-evident packaging measures, such as security labels, that help customers quickly identify whether a shipped device may have been opened or altered before installation.
Hardware-Based Protection Matters
Sachin explains that IQSIGHT has used hardware-based encryption and cryptographic co-processors in its products for many years. These protections are not reserved only for premium models. Instead, they are applied broadly across the portfolio.
That matters because security systems are rarely made up of one device type. A customer may use high-end cameras in some locations and lower-cost devices in others. If the security posture is inconsistent across the product line, weaker devices can create weak points in the overall system.
The point for end users, consultants, and integrators is simple: when evaluating security devices, it is not enough to ask whether encryption exists. It is also worth asking whether the manufacturer applies the same security philosophy across the full range of products.
Security by Design Is More Than a Marketing Phrase
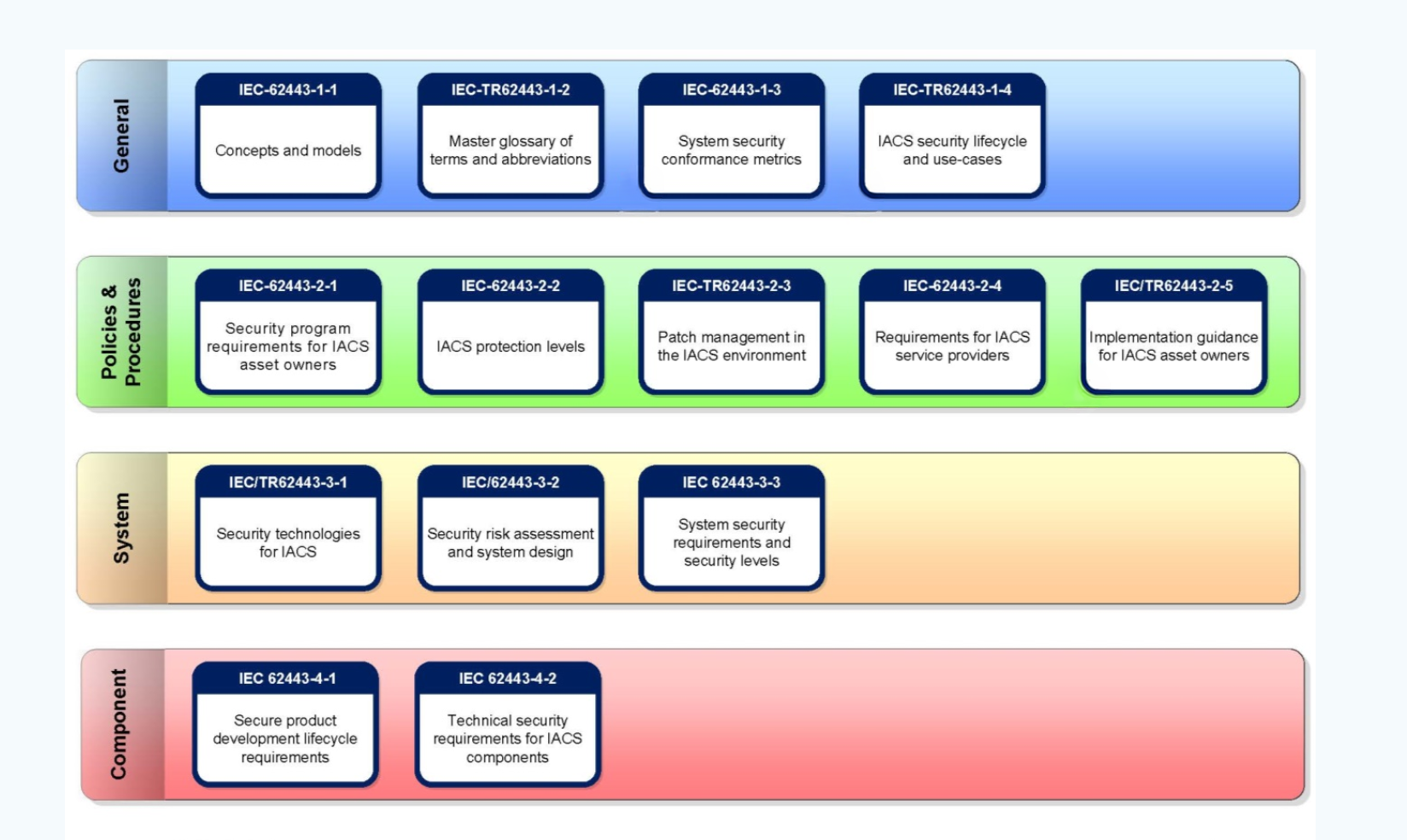
Sachin also highlights the role of secure development practices. He explains that IQSIGHT follows a security-by-design approach and aligns with recognized industry standards for cybersecurity governance and secure product development.
That is important because cybersecurity is not just about the final device. It is also about the development process behind that device. Strong governance, repeatable design practices, regular reviews, and formal security standards all help reduce the chance of avoidable weaknesses making their way into deployed products.
For customers, this means vendor selection should include more than performance specs and price. It should also include evaluating whether the manufacturer has a proven history of cybersecurity discipline, formal processes, and a track record of maintaining product trust over time.
Long-Term Trust Requires Ongoing Updates
Even when a device is designed and delivered securely, cybersecurity work does not stop. Sachin explains that trusted devices still need ongoing support through formal upgrades and security patches when new vulnerabilities are identified.
He notes that IQSIGHT gives customers the ability to load their own certificates onto supported devices, helping those devices become part of the customer’s own trusted environment. That is an important part of long-term risk management, especially in high-security settings where maintaining trust over the entire life of the device is critical.
For security professionals, that reinforces an important lesson: a secure device should not be viewed as a one-time purchase decision. It should be viewed as part of an ongoing lifecycle that includes updates, certificate management, vulnerability response, and vendor support.
What Security Professionals Should Be Asking Suppliers
This conversation points to several practical questions security professionals should ask when evaluating cameras and IoT devices:
-
How is the product secured during manufacturing?
-
How are components sourced and verified?
-
What protections exist against tampering during shipping and storage?
-
Does the device use hardware-based cryptographic protection?
-
Are security features consistent across the full product line?
-
Does the manufacturer follow recognized cybersecurity development standards?
-
How are patches, certificates, and long-term updates handled?
These questions are especially relevant for government, enterprise, and critical infrastructure environments where devices may not be exposed directly to the public internet, yet still must be trusted for many years after installation.
As connected security devices continue to spread across physical security environments, cybersecurity can no longer be separated from supply chain integrity. The device itself, the way it is made, the way it is shipped, and the way it is maintained all matter.
The discussion between Tom and Sachin is a reminder that true device trust is built in layers. It depends on secure design, secure manufacturing, secure logistics, hardware-based protections, and long-term vendor support.
For end users and system designers, the lesson is straightforward: do not just ask what a device can do. Ask how it was protected before it ever reached your network
Contact us for system design assistance >>
FAQ
Why is supply chain security important for IoT devices?
Because a device can be compromised before installation through counterfeit parts, tampering, or poor manufacturing security.
What is hardware-based encryption in security devices?
It is a security approach that uses built-in cryptographic hardware or co-processors to protect certificates, firmware, and device identity.
Why should security professionals ask about manufacturing practices?
Because secure design alone is not enough if a product can be altered during sourcing, production, shipping, or warehousing.
What makes a security camera trustworthy over time?
A combination of secure design, trusted manufacturing, tamper protection, certificate support, and regular security updates.