Matt and Ari attended the 2018 Smart and Secure Cities and Communities Conference.
2018 Global City Teams Challenge (GCTC) is co-hosted by NIST and U.S. Department of Homeland Security Science and Technology Directorate (DHS S&T) as the Smart and Secure Cities and Communities Challenge (SC3).
GCTC-SC3 kickoff conference brings together hundreds of municipal governments and technology innovators around the world with the goal to establish teams to address shared issues faced by cities and communities.
2018 round encourages participating teams to have additional focus on cybersecurity and privacy as the first order concern, as well as all existing GCTC goals such as replicability, scalability and sustainability.
What are government leaders, Chief Information Security Officers, and security professionals worried about?
We sat down with Bosch Security Systems' Network Video and Cyber Security Training Engineer, David Brent, to discuss how cyber security vulnerability across the electronic security system industry can impact businesses, organizations, and government.
Locking down all the devices beyond simple password protection is critically important. Applying passwords comes after selecting a trusted security manufacturer and as the first step of many when locking down IP cameras and other electronic security devices.
Target had a data security breach which compromised 40 million customer records. Craft and hobby store, Michaels, has 2.6 million records stolen. The University of Maryland had 300,000 records stolen. 20,000 patient records were stolen from Standford Hospital. Federal records show that the U.S. Federal Reserve detected more than 50 cyber security breaches between 2011 and 2015, including several incidents considered to be espionage, according to the Security Industry Association story. The Fed’s cyber security team logged 310 incident reports during the four-year span, 140 of which were classified as hacking attempts, reported Reuters. More on this by Reuters.
IP cameras and other devices present a network penetration risk
Reputable and trusted security manufacturers, like Bosch Security Systems, are meeting IT's cyber security demands. Here's how:

Request Security System Design Support from our Team
Not sure how vulnerable your connected devices might be? Meet Dr. Agn Cui from Red Balloon:
Bosch IP Video and Cyber Security
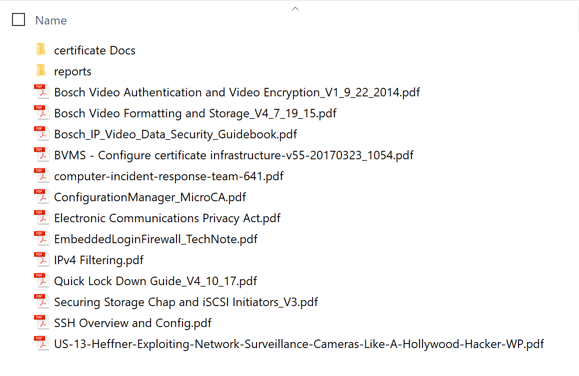
Cyber Security of IP Video Class Resources (available to class attendees)
LINK: Bosch Security Academy
RELATED CLASS: Expert Certification for BVMS is being held in Lancaster, PA Feb 6-9
This course provides the core competencies and knowledge an integrator or installer needs to successfully install and configure Bosch Video Management System using the Divar IP storage appliance. This course includes product demonstrations, in depth configurations, hardware installation, software overview, and troubleshooting.
In this training plan you will have multiple segments to complete for the certification. This includes an online prerequisite course, a classroom course, and the final exam.
Classroom (3.5 Days) Register Here
Download Cyber Security Resources
- IP Camera Lockdown Guide
- Network Authentication - 802.1X
- 3 Common Security Hacks
- Data Security Leaflet
- Securing Data and Equipment Racks
- Intrusion Detection System Encryption
- Security of Security
- Security Encryption and Certificates FAQ
- Lessons learned: major health care data breaches
- IT Advancements Revolutionizing Security Technology: Webinar on Demand
- NIST National Cybersecurity Center of Excellence
Government-Specific Resources
- Physical Security Solutions for US Federal Government Applications White Paper
- PKI CHAVE One-Page
- PKI CHAVE Leaflet
- PKI CHAVE Presentation PPT
Physical & Electronic Security Converged with Cyber Security
IT professionals can lock down and monitor equipment racks to preserve hardware integrity, and keep rogue laptops and removable storage devices away from the network and sensitive data. For example, consider how Edward Snowden stole information from the NSA via unprotected computer hardware. (story link here)
Equipment racks are located in dedicated IT closets and data centers. Cause for concern is the amount of IT hardware and infrastructure housed in closets that are shared and accessed by personnel from other departments. In this video we discuss several applications and options for securing data racks and closets.
CASE STUDY: securing data racks in York, PA
Consider the Bosch Training Academy or MidChes Professional Services for further information, education, and support.