Ari Erenthal, the MidChes intrusion alarm specialist for our team, evaluated the current status and reliability of using telephone (POTS) lines for modern security alarm communications. We've written many articles over the past few years about the growing concern and reliability of telephone lines and it was time for an update.
The video below is a great overview that Ari provided to Matt during a recent discussion about the topic.
Want the Alarm over IP White Papers? Scroll to the bottom of this article >>
The problem is that many in the security profession are convinced that, 1) switching from POTS to IP communication is a future problem, and 2) that they can continue to use telephone lines as long as they have copper at the premises. And it's not just copper that's the problem, fiber segments of the telephone line system present a new range of problems. Just because the alarm panel is connected to copper at the premises doesn’t mean that there is no fiber in the mix miles away. Just a single mile of fiber makes the entire communication link as unreliable as end-to-end fiber or copper.
Several of our prior posts, which were accurate when written, state that fiber is "a tomorrow problem." We now propose that fiber is "a today problem," and security professionals should be actively transitioning alarm panels to digital communication methods right now.
Ari summarized, "It is my opinion that POTS dialers should be upgraded as soon as possible, as they are about to become unreliable."
Time To Stop Monitoring Your Alarm Panels Via Telephone Lines
For an intrusion detection system to drive a response, it must be able to communicate. Until recently, alarm systems communicated by transmitting tones through telephone lines monitored by a central station. However, changes to the telephone grid in the United States are making this method less reliable. Therefore, many security consumers are choosing alternate, more reliable methods of alarm signal communications.
Background
Dual-tone multi-frequency signaling, also known as DTMF or Touch-Tone, is a method of sending a set of sixteen unique sounds, or tones. These tones represent the ten digits, the letters A to D, and the symbols # and *.
The on-site alarm panel uses a microcomputer that decides if and when to communicate to the central monitoring station. The panel takes over the phone line, dials, waits for the call to be answered by a computer at the central station, and sends a series of tones. This series of tones has many names, however is most commonly referred to as a signal. The computer at the central station, called a receiver, interprets the signal and brings up associated information on an operator’s computer along with previously defined instructions for how to proceed given the specific alarm.
How A Panel Sends A Signal
When a receiver answers a call from an alarm panel, it first sends a signal called a handshake to let the panel know that it is ready to receive information. This handshake typically takes a tenth of a second. The panel then sends its alarm signal to the receiver. The signal takes the form of a series of tones representing the name and location of the subscriber, the details of the signal, and the ID of the origination point. This is followed by a checksum tone, to ensure that the signal came through clearly and was not corrupted in transmission. This signal typically takes 1.5 to 2 seconds to transmit. The receiver then sends a signal called a kissoff, letting the panel know that the signal was received so it can stop transmitting and release the line.
The specific method the panel uses to communicate is called a reporting format. Reporting formats vary from manufacturer to manufacturer, but the format most commonly used to monitor intrusion detection and fire alarm systems is called Contact ID.
How A Telephone Call Is Transmitted
When a call is placed over copper infrastructure, an analog signal is picked up by the microphone on one end, transmitted over a pair of wires through as many switches and exchanges as necessary, and outputs on a speaker on the other end. The signal is 1:1, with a physical connection required between caller and listener. The sound picked up by the microphone, or generated by the alarm panel, is reproduced as exactly as possible by the speaker on the other end of the call.
When a call is placed over fiber infrastructure, the sound is picked up by the microphone on one end, digitized, transmitted over network, and then replayed through the speaker on the other end. The signal is not 1:1. The process of digitization compresses the signal, which causes a tiny amount of loss that is generally not noticeable to the human ear. This compression saves a significant amount of bandwidth, making fiber infrastructure more efficient than copper.
Telecom Infrastructure Being Replaced By Fiber
The millions of miles of copper cables that connect all the telephone exchanges in the United States to each other are gradually being replaced with fiber cables and digital processing equipment. Fiber allows for faster transmission of far more simultaneous signals than copper and allows for a much more resilient broadband architecture. Telecom companies are enthusiastically embracing fiber and replacing the copper backbone in this country. The pace of this adoption has been slow, because telecom companies are required to seek approval from the FCC before transitioning to fiber in each market. However, once this approval is granted, the actual replacement process tends to be fast. State and federal regulators often require the telecom to notify their subscribers before transitioning them, but these notifications are often easy to miss and tend to be ignored.
Telecoms often use a multistage process called FTTX (Fiber to the X) to replace copper infrastructure. This process describes a method of slowly replacing a portion of the infrastructure. Fiber to the node (FTTN), fiber to the cabinet (FTTC), fiber to the premises (FTTP), and fiber to the home (FTTH) describes the steps needed to completely replace the entire communications pathway with fiber. Telecoms often are not required to notify service subscribers until the final stage of the project.
Fiber Presents A Challenge To Alarm Monitoring
Alarm reporting formats require a handshake and a kissoff from the gateway so that the panel knows when to start and stop transmitting, as well as a checksum to ensure that the signal was not corrupted in some way. However, when the signal is digitized and compressed by fiber equipment, the signal may not be transmitted or received reliably. Sometimes the handshake, checksum, or kissoff is chopped off or compromised. Some alarm panels allow a technician to program a slower reporting transmission speed, which makes the compression have less impact. However, this is unreliable. The precise amount of compression is unpredictable and depends on the exact route the call takes. Therefore, slowing the transmission speed doesn’t always work, or work reliably. In addition, the slower the transmission speed, the higher the chance that the signal will be interrupted or that the telephone line will be compromised, which is why signals were designed to be sent quickly in the first place.
Worse, security professionals can no longer be sure that their alarm signals will never be digitized on its way to the central station. Because telecoms use the FTTX, there is a good likelihood that the signal will pass a fiber node somewhere, even if the premises still has a copper connection.
Digital Monitoring Methods Are Now More Reliable Than Analog Ones
For this reason, many systems designers are using an all-digital monitoring method, using IP or cellular communications to connect to a central station.
 Bosch’s B series and new G series alarm panels come with an onboard Ethernet port, allowing integrators to monitor these panels over a network connection without purchasing additional equipment. These panels also come with an additional communication board slot for a cellular communicator. The B series comes with one modular slot and the new G series comes with two slots. These cellular communicators can be set as a sole, primary, or secondary communications path in the programming.
Bosch’s B series and new G series alarm panels come with an onboard Ethernet port, allowing integrators to monitor these panels over a network connection without purchasing additional equipment. These panels also come with an additional communication board slot for a cellular communicator. The B series comes with one modular slot and the new G series comes with two slots. These cellular communicators can be set as a sole, primary, or secondary communications path in the programming.
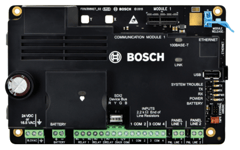 For existing installations, the new B465 Universal Dual Path Communicator converts almost any intrusion detection panel or fire alarm control panel to digital, even 3rd party panels. It is compatible with panels using Contact ID, SIA, Pulse 3/1 or Pulse 4/2, Modem II, Modem IIe, and Modem IIIa2 communication formats (auto detecting) and requires no panel programming. It supports IP directly and has one modular slot for a communication board for a cellular communicator. It is UL listed and approved for commercial burglary and fire alarm applications as a primary, secondary, or sole communications path.
For existing installations, the new B465 Universal Dual Path Communicator converts almost any intrusion detection panel or fire alarm control panel to digital, even 3rd party panels. It is compatible with panels using Contact ID, SIA, Pulse 3/1 or Pulse 4/2, Modem II, Modem IIe, and Modem IIIa2 communication formats (auto detecting) and requires no panel programming. It supports IP directly and has one modular slot for a communication board for a cellular communicator. It is UL listed and approved for commercial burglary and fire alarm applications as a primary, secondary, or sole communications path.
Assistance
This topic can be confusing and a decision to wait on the transition to IP can have an adverse impact on an organization. Our team is here to help understand the situation and guide end users and security dealers along the path to next-gen communication paths.
Security of Alarm Communications White Paper - Request Here >>









